Download Palo Alto Networks Certified Network Security Analyst.NetSec-Analyst.ExamTopics.2026-04-08.15q.tqb
| Vendor: | Palo Alto Networks |
| Exam Code: | NetSec-Analyst |
| Exam Name: | Palo Alto Networks Certified Network Security Analyst |
| Date: | Apr 08, 2026 |
| File Size: | 118 KB |
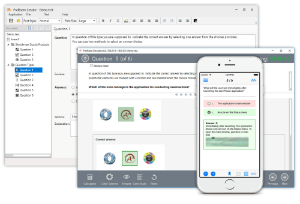
How to open TQB files?
Files with TQB (Taurus Question Bank) extension can be opened by Taurus Exam Studio.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
Which set of actions will allow an administrator to handle traffic redirection most efficiently when degradation occurs on a specific SaaS application that has an on-premises backup?
- Use Advanced Routing Engine to create a logical router with BGP, then set up a new AS routing environment. Peer the AS to the SaaS company's AS and redistribute routes from the SaaS company's AS with BGP Filtering profile for the application-specific traffic.
- Use VPN tunneling to create tunnels between the branches and the SaaS application provider with a backup tunnel pointing to the on-premises backup. Use OSPF to determine the shortest path to reach the application which will reconverge when there is a failure.
- Use Policy-Based Forwarding (PBF) to create a rule that sends sessions for the SaaS application to the on-premises backup, then create a path monitor with "wait-recover" selected. Ensure that "enforce symmetric return" is enabled for the rule so failures do not create routing loops.
- Use Advanced SD-WAN to create SaaS Quality profiles and Path Quality profiles with appropriate SLA levels, then create a Traffic Distribution profile set for "top down" with a DIA interface first and the SD-WAN path that leads to on-premises backup second. Use these in an SD-WAN rule.
Correct answer: D
Question 2
A firewall administrator is creating an application override rule to bypass Layer 7 inspection for a pre-defined application.
What is the expected behavior for Content-ID checks for this application?
- DNS Security will have degraded performance for advanced features.
- WildFire will only use inline-ML checks instead of sending items to WildFire Cloud.
- No additional security checks will occur due to there being only Layer 4 handling.
- Threat inspection will occur if the pre-defined application supports threat inspection.
Correct answer: C
Question 3
A Palo Alto Networks NGFW for a high-security environment is being configured and requires a security profile group that includes vulnerability protection.
When configuring the action based on the severity of the threat types, what does Palo Alto Networks recommend?
- Use action "allow" for critical high, and medium vulnerabilities.
- Use action "alert" for critical, high, and medium vulnerabilities.
- Use action "default" for critical, high, and medium vulnerabilities.
- Use action "reset-both" for critical, high, and medium vulnerabilities.
Correct answer: C
Question 4
A security administrator is creating an internet of things (IoT) Security policy and needs to select behaviors for the trafficю
Which characteristic has the greatest impact to the risk level of applications?

- Used by Malware
- Pervasive
- Tunnels Other Apps
- Known Vulnerabilities
Correct answer: A
Question 5
A security administrator is building out Decryption policies and wants to decrypt according to Palo Alto Networks best practices.
Which URL categories should the administrator add to the policies?
- Proxy avoidance and anonymizers, ransomware unknown, web-based email, web advertisements, and not resolved.
- Online storage and backup web-based email web hosting, personal sites and blogs, content delivery networks, and high-risk URL.
- AI website generator, Command and Control, compromised website, encrypted DNS, and dynamic DNS.
- Newly registered domains, internet communications and telephony, high-risk URL, insufficient content, hacking, and grayware.
Correct answer: D
Question 6
A team of analysts uses four NGWFs with the Precision Al Bundle, SaaS Security Inline, and Strata Cloud Manager Pro Collectively this secures all company assets across the data center and two remote sites. A security incident requires the team to review a mobile user, John Doe.
During the audit, the team prompts, "How was the application experience for John Doe over the past 60 days?”
What is an expected response from Strata Copilot?
- "The average application test score for 'john doe’ over the past 60 days is 37 67."
- The user ’John Doe' encountered a total of 219 threats in the last 3 hours."
- The top three threats impacting John Doe are phishing, SQL injections, and ransomware."
- "Your organization doesn’t have ADEM."
Correct answer: D
Question 7
A security administrator wants to determine which action a URL Filtering profile will take on the URL "www.chatgpt.com." The firewall has a custom URL object with "www.chatgpt.com/" as a member called "Permitted-AI." The URL "www.chatgpt.com" is also categorized as "Artificial-Intelligence, " "Computer-and-Internet-Info," and "Low-Risk." The URL Filtering profile has the following in descending order:
- Artificial-Intelligence set to continue
- Computer-and-Internet-Info set to block
- Low-Risk set to alert
- Permitted-AI set to allow
Which action will the URL Filtering profile take when traffic matches the "www.chatgpt.com" URL on a rule with this profile attached?
- Continue
- Alert
- Allow
- Block
Correct answer: C
Question 8
A financial company is deploying NGFWs with the Advanced SD-WAN subscription to improve uptime and bandwidth across thousands of ATMs. The company requires that traffic flows to the internal application needed by the ATMs always use the path with the lowest latency and packet loss.
Which unique SD-WAN rule parameters meet this criteria?
- Application/Service: "Internal Application for ATMs" → Path Selection: "Best Available Path" in Traffic Distribution Profile.
- Application/Service: "Internal Application for ATMs" & "Management" in Path Quality Profile → Path Selection "Any."
- Application/Service: "Internal Application for ATMs" → Path Selection "Weighted Distribution" in Traffic Distribution Profile.
- Application/Service: "Internal Application for ATMs" & "ATM Path(Custom)" in Path Quality Profile → Path Selection "Any."
Correct answer: A
Question 9
Which action ensures that a Panorama push will not fail due to pending local firewall changes?
- Commit configurations locally on the device and then repeat the same configuration from Panorama.
- Disable "Merge with Device Candidate Config."
- Enable "Force Template Values."
- Enable both options "Include Device and Network Templates" and "Include Firewall Clusters."
Correct answer: A
Question 10
What are two valid pattern types in a Data Filtering profile? (Choose two.)
- Custom Dictionary
- Proximity Pattern
- File Properties
- Regular Expression
Correct answer: B, D
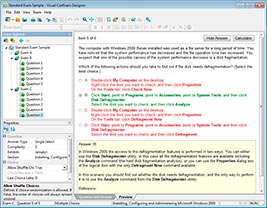
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files
HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files
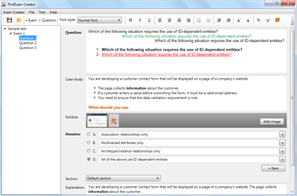
ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



