Download Oracle Cloud Infrastructure 2025 Networking Professional.1Z0-1124-25.Actual4Test.2026-04-24.117q.tqb
| Vendor: | Oracle |
| Exam Code: | 1Z0-1124-25 |
| Exam Name: | Oracle Cloud Infrastructure 2025 Networking Professional |
| Date: | Apr 24, 2026 |
| File Size: | 725 KB |
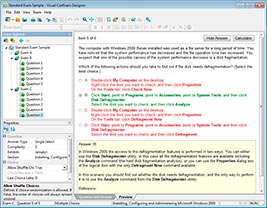
How to open TQB files?
Files with TQB (Taurus Question Bank) extension can be opened by Taurus Exam Studio.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
Your company is migrating an on-premises application to OCI. The application requires direct, low-latency access to an on-premises Microsoft SQL Server database. You've established a FastConnect connection between your on-premises network and an OCI VCN via a Dynamic Routing Gateway(DRG). You want to access this database from the OCI VCN. Which type of endpoint, in conjunction with appropriate routing, should you use to facilitate this connection?
- An Internet Gateway with a public endpoint on the SQL Server.
- A Service Gateway configured to access the on-premises SQL Server.
- No specific OCI endpoint is required. The on-premises SQL Server is accessed directly through the DRG and appropriate routing.
- A Private Endpoint within the VCN configured to connect to the private IP address of the on-premises SQL Server.
Correct answer: C
Explanation:
* Requirement: Low-latency, direct access to an on-premises SQL Server via FastConnect.* Option A: Internet Gateway with a public endpoint exposes the SQL Server to the internet, increasing latency and security risks-incorrect.* Option B: Service Gateway is for OCI services (e.g., Object Storage), not on-premises resources- incorrect.* Option C: FastConnect with a DRG provides a private, low-latency link. No additional OCI endpoint is needed; the SQL Server's private IP is accessed directly via DRG routing-correct.* Option D: Private Endpoints are for OCI services within the VCN (e.g., ADB), not on-premises resources-incorrect.* Conclusion: Option C leverages FastConnect and DRG for direct, secure access.Oracle documentation notes:* "FastConnect with a DRG enables private, low-latency connectivity to on-premises networks.Configure route tables to access on-premises resources directly; no additional endpoints are required." This supports Option C. Reference:FastConnect Overview - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/Network/Tasks/fastconnect.htm). * Requirement: Low-latency, direct access to an on-premises SQL Server via FastConnect.
* Option A: Internet Gateway with a public endpoint exposes the SQL Server to the internet, increasing latency and security risks-incorrect.
* Option B: Service Gateway is for OCI services (e.g., Object Storage), not on-premises resources- incorrect.
* Option C: FastConnect with a DRG provides a private, low-latency link. No additional OCI endpoint is needed; the SQL Server's private IP is accessed directly via DRG routing-correct.
* Option D: Private Endpoints are for OCI services within the VCN (e.g., ADB), not on-premises resources-incorrect.
* Conclusion: Option C leverages FastConnect and DRG for direct, secure access.
Oracle documentation notes:
* "FastConnect with a DRG enables private, low-latency connectivity to on-premises networks.
Configure route tables to access on-premises resources directly; no additional endpoints are required." This supports Option C. Reference:FastConnect Overview - Oracle Help Center(docs.oracle.com/en-us
/iaas/Content/Network/Tasks/fastconnect.htm).
Question 2
You are troubleshooting a BGP peering issue between your on-premises router and an OCI FastConnect virtual circuit. You have verified the physical connectivity and confirmed that the BGP session is established.
However, routes are not being exchanged. You suspect a problem with the BGP configuration. What is the MOST LIKELY cause of this issue, assuming the basic BGP configuration (AS numbers, peer IP addresses) is correct?
- The BGP keepalive timers are misconfigured, causing the session to drop intermittently.
- There is a mismatch in the BGP authentication keys between the on-premises router and OCI.
- The advertised prefixes are being filtered by a prefix list or route map on either the on-premises router or the OCI FastConnect virtual circuit.
- The MTU (Maximum Transmission Unit) size is mismatched, causing fragmentation and packet loss.
Correct answer: C
Explanation:
* Problem Context: BGP session is established, but no routes are exchanged, and basic config (ASNs, IPs) is correct.* Option A Analysis: Misconfigured keepalive timers would cause the session to drop intermittently.Since the session is confirmed as established, this is unlikely. Keepalives affect session stability, not route exchange.* Option B Analysis: A mismatch in BGP authentication keys (e.g., MD5 passwords) would prevent the session from establishing. Given the session is up, this is not the issue.* Option C Analysis: BGP prefix lists or route maps filter advertised routes. If either the on-premises router or OCI applies a filter (intentionally or misconfigured), it could block route advertisements despite an established session. This is a common issue in BGP setups and aligns with the symptoms.* Option D Analysis: MTU mismatches could cause packet loss or fragmentation, but BGP uses TCP (small packets), and session establishment indicates MTU isn't the primary issue. Route exchange failures are more likely due to filtering than MTU.* Conclusion: Option C is the most likely cause, as filtering directly prevents route exchange without affecting session status.From Oracle's FastConnect documentation:* "Once a BGP session is established, routes are exchanged based on the prefixes advertised by each side.Route maps, prefix lists, or filters on either the CPE or OCI side can restrict which routes are advertised or accepted."* "If no routes appear in the routing table despite an active session, verify that no filters are blocking advertisements."This supports Option C as the most likely cause. Reference:FastConnect Overview - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/Network/Tasks/fastconnect.htm). * Problem Context: BGP session is established, but no routes are exchanged, and basic config (ASNs, IPs) is correct.
* Option A Analysis: Misconfigured keepalive timers would cause the session to drop intermittently.
Since the session is confirmed as established, this is unlikely. Keepalives affect session stability, not route exchange.
* Option B Analysis: A mismatch in BGP authentication keys (e.g., MD5 passwords) would prevent the session from establishing. Given the session is up, this is not the issue.
* Option C Analysis: BGP prefix lists or route maps filter advertised routes. If either the on-premises router or OCI applies a filter (intentionally or misconfigured), it could block route advertisements despite an established session. This is a common issue in BGP setups and aligns with the symptoms.
* Option D Analysis: MTU mismatches could cause packet loss or fragmentation, but BGP uses TCP (small packets), and session establishment indicates MTU isn't the primary issue. Route exchange failures are more likely due to filtering than MTU.
* Conclusion: Option C is the most likely cause, as filtering directly prevents route exchange without affecting session status.
From Oracle's FastConnect documentation:
* "Once a BGP session is established, routes are exchanged based on the prefixes advertised by each side.
Route maps, prefix lists, or filters on either the CPE or OCI side can restrict which routes are advertised or accepted."
* "If no routes appear in the routing table despite an active session, verify that no filters are blocking advertisements."This supports Option C as the most likely cause. Reference:FastConnect Overview - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/Network/Tasks/fastconnect.htm).
Question 3
You are configuring a VCN with multiple subnets for a customer. The security team requires that all instances have IPv6 addresses. You configure the VCN with an IPv6 ULA CIDR block of fc00:1:1::/48 and create two private subnets. After launching instances in the two private subnets, you notice that they only have IPv4 addresses assigned. You have not manually configured any IPv6 addresses on the instances themselves. What steps are necessary to ensure the instances automatically receive IPv6 addresses?
- No further steps are needed. Instances will automatically receive IPv6 addresses within the configured subnets upon launch.
- Ensure that SLAAC (Stateless Address Autoconfiguration) is enabled on the operating system of the instances within the two subnets.
- IPv6 address assignment is only supported on instances launched in public subnets.
- Make sure the "Assign public IPv4 address" option is not selected during instance creation. This will force the instance to default to IPv6 allocation.
Correct answer: B
Explanation:
* Problem:Instances lack IPv6 addresses despite VCN IPv6 configuration.* OCI IPv6 Behavior:IPv6 requires subnet enablement and OS support via SLAAC.* Evaluate Options:* A:Incorrect. OCI doesn't auto-assign IPv6 without OS configuration.* B:Correct. SLAAC must be enabled on the instance OS for auto-assignment.* C:Incorrect. IPv6 works in both public and private subnets.* D:Incorrect. IPv4 and IPv6 assignments are independent.* Conclusion:Enabling SLAAC on the OS ensures automatic IPv6 assignment.IPv6 in OCI relies on SLAAC for automatic address assignment. The Oracle Networking Professional study guide states, "To enable IPv6 on instances, the VCN and subnet must have IPv6 CIDR blocks, and the instance OS must support SLAAC to automatically configure IPv6 addresses" (OCI Networking Documentation, Section: IPv6 Configuration). Without SLAAC, instances default to IPv4 only. * Problem:Instances lack IPv6 addresses despite VCN IPv6 configuration.
* OCI IPv6 Behavior:IPv6 requires subnet enablement and OS support via SLAAC.
* Evaluate Options:
* A:Incorrect. OCI doesn't auto-assign IPv6 without OS configuration.
* B:Correct. SLAAC must be enabled on the instance OS for auto-assignment.
* C:Incorrect. IPv6 works in both public and private subnets.
* D:Incorrect. IPv4 and IPv6 assignments are independent.
* Conclusion:Enabling SLAAC on the OS ensures automatic IPv6 assignment.
IPv6 in OCI relies on SLAAC for automatic address assignment. The Oracle Networking Professional study guide states, "To enable IPv6 on instances, the VCN and subnet must have IPv6 CIDR blocks, and the instance OS must support SLAAC to automatically configure IPv6 addresses" (OCI Networking Documentation, Section: IPv6 Configuration). Without SLAAC, instances default to IPv4 only.
Question 4
Which aspect of OCI's security framework is essential for continuous monitoring and verification of packet flows, a core requirement of Zero Trust Packet Routing?
- Static routing configurations
- Default security lists
- Flow logs and audit trails
- Public IP address assignments
Correct answer: C
Explanation:
* Goal: Support Zero Trust with packet flow monitoring.* Option A: Static routing defines paths, not monitoring-incorrect.* Option B: Security lists control access, not monitor-incorrect.* Option C: Flow logs track traffic; audit trails log actions-essential for Zero Trust-correct.* Option D: Public IPs enable access, not monitoring-incorrect.* Conclusion: Option C is essential.Oracle states:* "Flow logs and audit trails provide continuous monitoring and verification of packet flows, critical for Zero Trust Packet Routing."This supports Option C. Reference:Zero Trust in OCI - Oracle Help Center (docs.oracle.com/en-us/iaas/Content/Network/Concepts/zerotrust.htm). * Goal: Support Zero Trust with packet flow monitoring.
* Option A: Static routing defines paths, not monitoring-incorrect.
* Option B: Security lists control access, not monitor-incorrect.
* Option C: Flow logs track traffic; audit trails log actions-essential for Zero Trust-correct.
* Option D: Public IPs enable access, not monitoring-incorrect.
* Conclusion: Option C is essential.
Oracle states:
* "Flow logs and audit trails provide continuous monitoring and verification of packet flows, critical for Zero Trust Packet Routing."This supports Option C. Reference:Zero Trust in OCI - Oracle Help Center (docs.oracle.com/en-us/iaas/Content/Network/Concepts/zerotrust.htm).
Question 5
Your company needs to establish a secure connection between your on-premises network and OCI for a pilot project. The project has a limited budget and requires a quick setup, but also demands that the connection is encrypted. The long-term plan involves migrating to FastConnect, but that will take several months. Which OCI VPN solution would be most suitable for this short-term, budget-conscious, and security-aware scenario?
- Use a Dynamic Routing Gateway (DRG) with a Site-to-Site VPN connection configured using static routing.
- Deploy a third-party virtual appliance VPN solution from the OCI Marketplace within a public subnet and configure a VPN connection to your on-premises network.
- Use a Service Gateway to connect to a third-party VPN service available on the internet.
- Use a Dynamic Routing Gateway (DRG) with a Site-to-Site VPN connection configured using dynamic routing with BGP.
Correct answer: A
Explanation:
* Requirements:Quick, cheap, encrypted VPN; interim before FastConnect.* VPN Options:* Static VPN:Simple, native, low cost.* Third-Party Appliance:Complex, costly.* Service Gateway:Not for VPN; incorrect.* BGP VPN:Dynamic, more setup; less quick.* Evaluate Options:* A:Static VPN is fast, secure, budget-friendly; correct.* B:Appliance adds cost and complexity; incorrect.* C:Misaligned use of Service Gateway; incorrect.* D:BGP is overkill for pilot; less efficient.* Conclusion:Static VPN via DRG is most suitable.Static VPN is ideal for quick setups. The Oracle Networking Professional study guide notes, "A Site-to-Site VPN with static routing via DRG provides a fast, encrypted connection for short-term needs, minimizing cost and setup time" (OCI Networking Documentation, Section: Site-to-Site VPN). This fits the pilot project perfectly. * Requirements:Quick, cheap, encrypted VPN; interim before FastConnect.
* VPN Options:
* Static VPN:Simple, native, low cost.
* Third-Party Appliance:Complex, costly.
* Service Gateway:Not for VPN; incorrect.
* BGP VPN:Dynamic, more setup; less quick.
* Evaluate Options:
* A:Static VPN is fast, secure, budget-friendly; correct.
* B:Appliance adds cost and complexity; incorrect.
* C:Misaligned use of Service Gateway; incorrect.
* D:BGP is overkill for pilot; less efficient.
* Conclusion:Static VPN via DRG is most suitable.
Static VPN is ideal for quick setups. The Oracle Networking Professional study guide notes, "A Site-to-Site VPN with static routing via DRG provides a fast, encrypted connection for short-term needs, minimizing cost and setup time" (OCI Networking Documentation, Section: Site-to-Site VPN). This fits the pilot project perfectly.
Question 6
You are a Cloud Architect troubleshooting connectivity issues in your OCI environment. Your application servers, residing in private subnets within a VCN, need to access Object Storage within the same region to retrieve critical data. You have confirmed that there are no NSG rules blocking traffic between the subnets.
However, the instances cannot access Object Storage. You have a Service Gateway configured, and route rules in the private subnets directing traffic for Oracle Services to the Service Gateway. What is the most likely cause of this issue?
- The Service Gateway is not configured with the correct service CIDR labels for Object Storage in the region.
- The Internet Gateway is disabled.
- The security list associated with the private subnet does not allow outbound traffic to all Oracle Services.
- The NAT Gateway is not configured correctly to access external services.
Correct answer: A
Explanation:
* Problem:Private subnet instances can't access Object Storage via Service Gateway.* Setup Check:Route rules point to Service Gateway; NSGs allow traffic.* Evaluate Causes:* A:Incorrect CIDR labels block Object Storage access; likely.* B:Internet Gateway irrelevant for Service Gateway; incorrect.* C:NSGs confirmed open, security lists secondary; less likely.* D:NAT Gateway not used here; incorrect.* Conclusion:Misconfigured Service Gateway CIDR is the most likely issue.Service Gateway requires specific CIDR labels. The Oracle Networking Professional study guide states, "For private subnets to access Object Storage via a Service Gateway, the gateway must be configured with the correct regional Oracle Services CIDR label" (OCI Networking Documentation, Section: Service Gateway Configuration). Misconfiguration prevents access despite proper routing. * Problem:Private subnet instances can't access Object Storage via Service Gateway.
* Setup Check:Route rules point to Service Gateway; NSGs allow traffic.
* Evaluate Causes:
* A:Incorrect CIDR labels block Object Storage access; likely.
* B:Internet Gateway irrelevant for Service Gateway; incorrect.
* C:NSGs confirmed open, security lists secondary; less likely.
* D:NAT Gateway not used here; incorrect.
* Conclusion:Misconfigured Service Gateway CIDR is the most likely issue.
Service Gateway requires specific CIDR labels. The Oracle Networking Professional study guide states, "For private subnets to access Object Storage via a Service Gateway, the gateway must be configured with the correct regional Oracle Services CIDR label" (OCI Networking Documentation, Section: Service Gateway Configuration). Misconfiguration prevents access despite proper routing.
Question 7
You are a cloud architect designing a multi-tiered application on OCI. One tier consists of publicly accessible web servers that must be protected from common web exploits. You plan to use OCI Network Firewall to achieve this. You need to configure the Network Firewall to detect and prevent SQL injection attacks against the web servers. Which Network Firewall feature is most suitable for this purpose?
- Stateful Inspection, configured with default IPS policies.
- Intrusion Detection and Prevention System (IDPS) signatures with custom rule sets for SQL injection.
- URL Filtering with predefined categories blocking SQL injection attempts.
- Geo-location filtering to block traffic from countries known for SQL injection attacks.
Correct answer: B
Explanation:
* Goal:Protect web servers from SQL injection using Network Firewall.* Firewall Features:* Stateful Inspection:Basic traffic tracking, limited exploit detection.* IDPS:Detects and prevents exploits via signatures.* URL Filtering:Blocks URLs, not payload-based attacks.* Geo-location:Blocks regions, not specific threats.* Evaluate Options:* A:Default IPS lacks SQL injection specificity; insufficient.* B:IDPS with custom signatures targets SQL injection; most suitable.* C:URL Filtering doesn't address SQL injection payloads; incorrect.* D:Geo-location is broad, not precise; ineffective.* Conclusion:IDPS with custom rules is the best feature.IDPS in OCI Network Firewall is designed for exploit prevention. The Oracle Networking Professional study guide explains, "The Intrusion Detection and Prevention System (IDPS) uses signatures to detect and block specific threats like SQL injection, with custom rule sets for tailored protection" (OCI Networking Documentation, Section: Network Firewall IDPS). This ensures precise defense against web exploits. * Goal:Protect web servers from SQL injection using Network Firewall.
* Firewall Features:
* Stateful Inspection:Basic traffic tracking, limited exploit detection.
* IDPS:Detects and prevents exploits via signatures.
* URL Filtering:Blocks URLs, not payload-based attacks.
* Geo-location:Blocks regions, not specific threats.
* Evaluate Options:
* A:Default IPS lacks SQL injection specificity; insufficient.
* B:IDPS with custom signatures targets SQL injection; most suitable.
* C:URL Filtering doesn't address SQL injection payloads; incorrect.
* D:Geo-location is broad, not precise; ineffective.
* Conclusion:IDPS with custom rules is the best feature.
IDPS in OCI Network Firewall is designed for exploit prevention. The Oracle Networking Professional study guide explains, "The Intrusion Detection and Prevention System (IDPS) uses signatures to detect and block specific threats like SQL injection, with custom rule sets for tailored protection" (OCI Networking Documentation, Section: Network Firewall IDPS). This ensures precise defense against web exploits.
Question 8
You are designing an OCI VCN for a new application with the following requirements: The application servers in a private subnet must be able to download software updates from public repositories on the internet; the application servers must NOT be directly accessible from the public internet; the application servers must also be able to access Oracle Cloud Infrastructure Registry (OCIR) within the same region to pull container images. Which combination of VCN Gateways BEST meets these requirements?
- Internet Gateway and Service Gateway
- NAT Gateway and Internet Gateway
- NAT Gateway and Service Gateway
- Dynamic Routing Gateway (DRG) and Internet Gateway
Correct answer: C
Explanation:
* Requirements: Outbound internet access, no inbound exposure, and private OCIR access.* Option A: Internet Gateway allows inbound traffic, violating the no-exposure rule-incorrect.* Option B: NAT Gateway enables outbound-only internet access, but Internet Gateway adds inbound exposure-incorrect.* Option C: NAT Gateway provides outbound internet access without inbound exposure; Service Gateway enables private OCIR access-correct.* Option D: DRG is for external networks, not internet/OCIR access; Internet Gateway exposes servers- incorrect.* Conclusion: Option C satisfies all requirements.Oracle states:* "Use a NAT Gateway for outbound internet access from private subnets without inbound connectivity.Use a Service Gateway for private access to OCI services like OCIR."This supports Option C.Reference:NAT and Service Gateway Overview - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/Network/Tasks/NATgateway.htm & docs.oracle.com/en-us/iaas/Content/Network/Tasks/servicegateway.htm). * Requirements: Outbound internet access, no inbound exposure, and private OCIR access.
* Option A: Internet Gateway allows inbound traffic, violating the no-exposure rule-incorrect.
* Option B: NAT Gateway enables outbound-only internet access, but Internet Gateway adds inbound exposure-incorrect.
* Option C: NAT Gateway provides outbound internet access without inbound exposure; Service Gateway enables private OCIR access-correct.
* Option D: DRG is for external networks, not internet/OCIR access; Internet Gateway exposes servers- incorrect.
* Conclusion: Option C satisfies all requirements.
Oracle states:
* "Use a NAT Gateway for outbound internet access from private subnets without inbound connectivity.
Use a Service Gateway for private access to OCI services like OCIR."This supports Option C.
Reference:NAT and Service Gateway Overview - Oracle Help Center(docs.oracle.com/en-us/iaas
/Content/Network/Tasks/NATgateway.htm & docs.oracle.com/en-us/iaas/Content/Network/Tasks
/servicegateway.htm).
Question 9
Your company is setting up a FastConnect connection with a provider. You have purchased a port from the provider, and they are requesting information to set up the connection to Oracle Cloud Infrastructure. They specifically require information to configure the VLANs. What information regarding VLAN configuration is ESSENTIAL for them to successfully establish the FastConnect circuit?
- The list of all VCN CIDR blocks and their associated tags.
- A single unused VLAN ID, your BGP ASN, and the BGP peering IP addresses you want to use.
- The MTU (Maximum Transmission Unit) size for all VNICs in your OCI tenancy.
- Your Oracle Cloud Identifier (OCID) and compartment ID.
Correct answer: B
Explanation:
* Requirement: Provide VLAN config info for FastConnect setup.* Option A: CIDR blocks are for routing, not VLAN setup-incorrect.* Option B: VLAN ID defines the circuit, BGP ASN and peering IPs establish routing-essential and correct.* Option C: MTU is a performance setting, not required for VLAN config-incorrect.* Option D: OCID and compartment ID are for OCI management, not provider setup-incorrect.* Conclusion: Option B provides the necessary VLAN configuration details.Oracle states:* "For FastConnect, provide the provider with a VLAN ID, your BGP ASN, and BGP peering IPs to configure the virtual circuit."This confirms Option B. Reference:FastConnect Configuration - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/Network/Tasks/fastconnect.htm#providerconfig). * Requirement: Provide VLAN config info for FastConnect setup.
* Option A: CIDR blocks are for routing, not VLAN setup-incorrect.
* Option B: VLAN ID defines the circuit, BGP ASN and peering IPs establish routing-essential and correct.
* Option C: MTU is a performance setting, not required for VLAN config-incorrect.
* Option D: OCID and compartment ID are for OCI management, not provider setup-incorrect.
* Conclusion: Option B provides the necessary VLAN configuration details.
Oracle states:
* "For FastConnect, provide the provider with a VLAN ID, your BGP ASN, and BGP peering IPs to configure the virtual circuit."This confirms Option B. Reference:FastConnect Configuration - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/Network/Tasks/fastconnect.htm#providerconfig).
Question 10
You are designing a microservices-based application on OCI. Each microservice is deployed as a container in Oracle Container Engine for Kubernetes (OKE). You want to expose these microservices through a single entry point using a Layer 7 load balancer and route traffic based on the request path. Which OCI load balancing integration method with OKE is the MOST appropriate and efficient?
- Manually create a Regional Load Balancer and configure backend sets with the private IP addresses of the Kubernetes worker nodes hosting the microservices.
- Deploy a Kubernetes LoadBalancer service, which automatically provisions an OCI Regional Load Balancer to distribute traffic to the microservice pods.
- Deploy a Kubernetes NodePort service for each microservice and configure an OCI NetworkLoad Balancer to forward traffic to the NodePort services on the worker nodes.
- Deploy a Kubernetes Ingress controller that leverages an OCI Regional Load Balancer to route traffic to the microservice pods based on Ingress rules.
Correct answer: D
Explanation:
* Goal: Layer 7 routing for OKE microservices via a single entry point.* Option A: Manual configuration is inefficient and doesn't support path-based routing-incorrect.* Option B: LoadBalancer service provisions a Layer 4 balancer, not Layer 7 path routing-incorrect.* Option C: NodePort with NLB is Layer 4, less secure, and lacks path routing-incorrect.* Option D: Ingress controller with Regional Load Balancer (Application LB) provides Layer 7 routing based on paths-correct and efficient.* Conclusion: Option D is the best integration method.Oracle states:* "Use a Kubernetes Ingress controller with OCI Regional Load Balancer for Layer 7 routing to OKE microservices based on request paths."This supports Option D. Reference:OKE Networking - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/ContEng/Tasks/contengnetworking.htm). * Goal: Layer 7 routing for OKE microservices via a single entry point.
* Option A: Manual configuration is inefficient and doesn't support path-based routing-incorrect.
* Option B: LoadBalancer service provisions a Layer 4 balancer, not Layer 7 path routing-incorrect.
* Option C: NodePort with NLB is Layer 4, less secure, and lacks path routing-incorrect.
* Option D: Ingress controller with Regional Load Balancer (Application LB) provides Layer 7 routing based on paths-correct and efficient.
* Conclusion: Option D is the best integration method.
Oracle states:
* "Use a Kubernetes Ingress controller with OCI Regional Load Balancer for Layer 7 routing to OKE microservices based on request paths."This supports Option D. Reference:OKE Networking - Oracle Help Center(docs.oracle.com/en-us/iaas/Content/ContEng/Tasks/contengnetworking.htm).
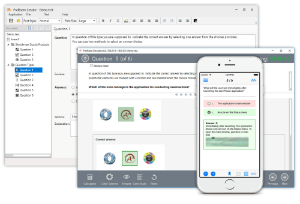
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files
HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files
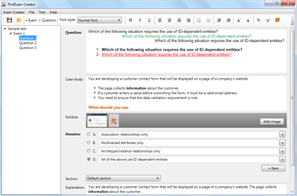
ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



