Download Certified Ethical Hacker v13.312-50v13.Marks4Sure.2026-03-14.390q.tqb
| Vendor: | ECCouncil |
| Exam Code: | 312-50v13 |
| Exam Name: | Certified Ethical Hacker v13 |
| Date: | Mar 14, 2026 |
| File Size: | 6 MB |
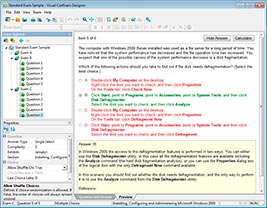
How to open TQB files?
Files with TQB (Taurus Question Bank) extension can be opened by Taurus Exam Studio.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
Under what conditions does a secondary name server request a zone transfer from a primary name server?
- When a primary SOA is higher that a secondary SOA
- When a secondary SOA is higher that a primary SOA
- When a primary name server has had its service restarted
- When a secondary name server has had its service restarted
- When the TTL falls to zero
Correct answer: A
Question 2
Which of the following is a component of a risk assessment?
- Administrative safeguards
- Physical security
- DMZ
- Logical interface
Correct answer: A
Question 3
Peter is surfing the internet looking for information about DX Company. Which hacking process is Peter doing?
- Scanning
- Footprinting
- Enumeration
- System Hacking
Correct answer: B
Question 4
An attacker, using a rogue wireless AP, performed an MITM attack and injected an HTML code to embed a malicious applet in all HTTP connections.
When users accessed any page, the applet ran and exploited many machines. Which one of the following tools the hacker probably used to inject HTML code?
- Wireshark
- Ettercap
- Aircrack-ng
- Tcpdump
Correct answer: B
Question 5
While using your bank’s online servicing you notice the following string in the URL bar:
“http: // www. MyPersonalBank. com/ account?id=368940911028389&Damount=10980&Camount=21”
You observe that if you modify the Damount & Camount values and submit the request, that data on the web page reflects the changes.
Which type of vulnerability is present on this site?
- Cookie Tampering
- SQL Injection
- Web Parameter Tampering
- XSS Reflection
Correct answer: C
Question 6
Which of the following algorithms can be used to guarantee the integrity of messages being sent, in transit, or stored?
- symmetric algorithms
- asymmetric algorithms
- hashing algorithms
- integrity algorithms
Correct answer: C
Question 7
What tool can crack Windows SMB passwords simply by listening to network traffic?
- This is not possible
- Netbus
- NTFSDOS
- L0phtcrack
Correct answer: D
Question 8
Bob, a system administrator at TPNQM SA, concluded one day that a DMZ is not needed if he properly configures the firewall to allow access just to servers/ports, which can have direct internet access, and block the access to workstations.
Bob also concluded that DMZ makes sense just when a stateful firewall is available, which is not the case of TPNQM SA.
In this context, what can you say?
- Bob can be right since DMZ does not make sense when combined with stateless firewalls
- Bob is partially right. He does not need to separate networks if he can create rules by destination IPs, one by one
- Bob is totally wrong. DMZ is always relevant when the company has internet servers and workstations
- Bob is partially right. DMZ does not make sense when a stateless firewall is available
Correct answer: C
Question 9
Based on the following extract from the log of a compromised machine, what is the hacker really trying to steal?
- har.txt
- SAM file
- wwwroot
- Repair file
Correct answer: B
Question 10
User A is writing a sensitive email message to user B outside the local network. User A has chosen to use PKI to secure his message and ensure only user B can read the sensitive email. At what layer of the OSI layer does the encryption and decryption of the message take place?
- Application
- Transport
- Session
- Presentation
Correct answer: D
Explanation:
https://en.wikipedia.org/wiki/Presentation_layerIn the seven-layer OSI model of computer networking, the presentation layer is layer 6 and serves as the data translator for the network. It is sometimes called the syntax layer. The presentation layer is responsible for the formatting and delivery of information to the application layer for further processing or display.Encryption is typically done at this level too, although it can be done on the application, session, transport, or network layers, each having its own advantages and disadvantages. Decryption is also handled at the presentation layer. For example, when logging on to bank account sites the presentation layer will decrypt the data as it is received. https://en.wikipedia.org/wiki/Presentation_layer
In the seven-layer OSI model of computer networking, the presentation layer is layer 6 and serves as the data translator for the network. It is sometimes called the syntax layer. The presentation layer is responsible for the formatting and delivery of information to the application layer for further processing or display.
Encryption is typically done at this level too, although it can be done on the application, session, transport, or network layers, each having its own advantages and disadvantages. Decryption is also handled at the presentation layer. For example, when logging on to bank account sites the presentation layer will decrypt the data as it is received.
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files
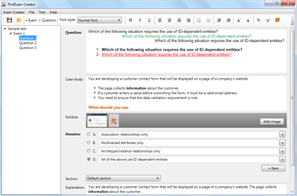
HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files
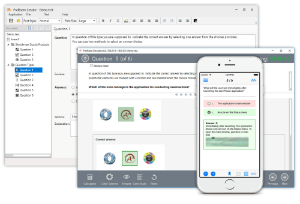
ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



