Download CompTIA SecurityX Certification.CAS-005.ExamTopics.2026-05-05.127q.tqb
| Vendor: | CompTIA |
| Exam Code: | CAS-005 |
| Exam Name: | CompTIA SecurityX Certification |
| Date: | May 05, 2026 |
| File Size: | 3 MB |
How to open TQB files?
Files with TQB (Taurus Question Bank) extension can be opened by Taurus Exam Studio.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
A security architect wants to ensure a remote host's identity and decides that pinning the X.509 certificate to the device is the most effective solution. Which of the following must happen first?
- Use Distinguished Encoding Rules (DER) for the certificate.
- Extract the private key from the certificate.
- Use an out-of-band method to obtain the certificate.
- Compare the retrieved certificate with the embedded certificate.
Correct answer: C
Question 2
A web application server is running a legacy operating system with an unpatched RCE vulnerability. The server cannot be upgraded until the corresponding application code is changed. Which of the following compensating controls would best prevent successful exploitation?
- Segmentation
- CASB
- HIPS
- UEBA
Correct answer: A
Question 3
An organization's board of directors has asked the Chief Information Security Officer to build a third-party management program. Which of the following best explains a reason for this request?
- Risk transference
- Supply chain visibility
- Support availability
- Vulnerability management
Correct answer: B
Question 4
A retail organization wants to properly test and verify its capabilities to detect and/or prevent specific TTPs as mapped to the MITRE ATTACK framework specific to APTs. Which of the following should be used by the organization to accomplish this goal?
- Tabletop exercise
- Penetration test
- Sandbox detonation
- Honeypot
Correct answer: B
Question 5
A systems administrator is working with the SOC to identify potential intrusions associated with ransomware. The SOC wants the systems administrator to perform network-level analysis to identify outbound traffic from any infected machines. Which of the following is the most appropriate action for the systems administrator to take?
- Monitor for IoCs associated with C&C communications.
- Tune alerts to Identify changes to administrative groups.
- Review NetFlow logs for unexpected increases in egress traffic.
- Perform binary hash comparisons to identify infected devices.
Correct answer: C
Question 6
Which of the following is the best way to protect the website browsing history for an executive who travels to foreign countries where internet usage is closely monitored?
- DOH
- EAP-TLS
- Geofencing
- Private browsing mode
Correct answer: A
Question 7
A security engineer receives reports through the organization's bug bounty program about remote code execution in a specific component in a custom application. Management wants to properly secure the component and proactively avoid similar issues. Which of the following is the best approach to uncover additional vulnerable paths in the application?
- Leverage an exploitation framework to uncover vulnerabilities.
- Use fuzz testing to uncover potential vulnerabilities in the application.
- Utilize a software composition analysis tool to report known vulnerabilities.
- Reverse engineer the application to look for vulnerable code paths.
- Analyze the use of an HTTP intercepting proxy to dynamically uncover issues.
Correct answer: B
Question 8
A security analyst is investigating a possible insider threat incident that involves the use of an unauthorized USB from a shared account to exfiltrate data. The event did not create an alert. The analyst has confirmed the USB hardware ID is not on the device allow list, but has not yet confirmed the owner of the USB device. Which of the following actions should the analyst take next?
- Classify the incident as a false positive.
- Classify the incident as a false negative.
- Classify the incident as a true positive.
- Classify the incident as a true negative.
Correct answer: B
Question 9
A software analyst is conducting a forensic investigation. The analyst needs to differentiate between approved software components and those used within an application If used as part of the CI/CD pipeline, which of the following would most effectively help the analyst do this?
- Dynamic analysis
- Branch protection
- Desenalization
- Code signing
Correct answer: D
Question 10
A company with a large, cloud-native, e-commerce website wants to know more details about an ongoing, sophisticated attack against the web platform. Which of the following is the best technique?
- User behavior analytics
- Dark web monitoring
- Structured Threat Information exchange
- High-interaction honeypots
Correct answer: D
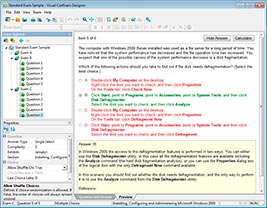
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files
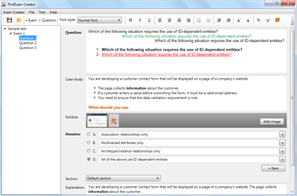
HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files
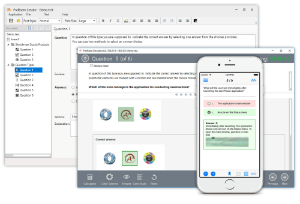
ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



